With the development of urbanization, the application of elevator in high-rise buildings is essential. The Monarch Elevator Control System is the most mature and reliable control system in the all-in-one system of elevator industries. The Monarch Elevator Control System is simple and reliable, and easy to maintain, but it has the password that makes the maintainer fall into difficulties. Monarch’s passwords are divided into user password, manufacturer password, implicit password (so-called dynamic password), and even super password. Today ElevatorVip will teach you guys how to unlock / remove the password of Monarch PCB boards, the tutorial as below:

Step.1: Must be controller powered off.
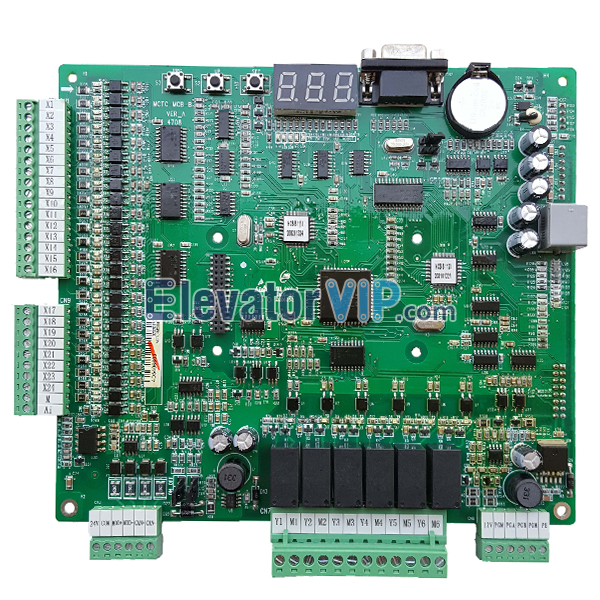
Step.2: Then check the motherboard’s version: MCTC-MCB-B, MCTC-MCB-C1, MCTC-MCB-C2, or MCTC-MCB-C3?
Step.3: If the version is MCTC-MCB-C1, MCTC-MCB-C2, and MCTC-MCB-C3, please take out the MCTC-PG card first.
Step.4: Find the clip number U45 on the motherboard.
Step.5: Check the clipping of Monarch Decoder Tool, make sure the No.1 of pin (red cable) is existed.
Step.6: Make sure the No.1 of pin of chip U45 on the motherboard has the point label (white color point).
Step.7: To clip the chip U45 use the Monarch decoder tool, make sure they are matched proper.
Step.8: If the pin chips are matched proper, then the motherboard’s display is lighting on, and LED of COP, LOP, and two others are lighting on.
Step.9: Select the model function on the Monarch decoder tool (press the black switch).
Step.10: For MCTC-MCB-C1, MCTC-MCB-C2, and MCTC-MCB-C3 board is selected on model: NICE 3000+(15.00)?.
Step.11: Then press the green color switch on the Monarch decoder tool to scan the old password.
Step.12: When seen the old password, release the chip clipper and turn on the controller power.
Step.13: Then press the password into the motherboard by Monarch Service Tool (Key pad).
All of above steps are completed to finish the decoding password of Monarch’s board password. If there have any questions, just contact ElevatorVip. Thank you!
The relevant accessories are shown below:
MCTC-MCB-B
Monarch Service Tool (Keypad)
Monarch Decoder Tool